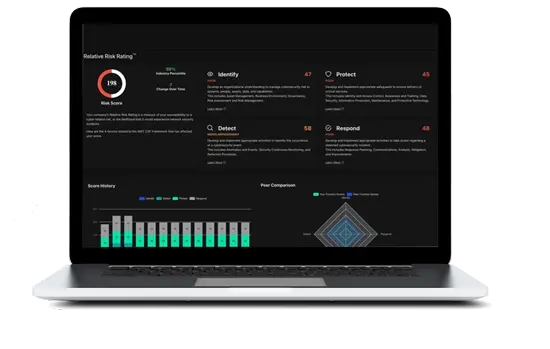
Relative Risk Rating (R3)
Every infrastructure element scored in real time using NIST Cybersecurity Framework guidelines. Prioritize what matters most based on your environment, industry cohort, and historical breach data.
Agentless discovery, real-time risk scoring, integrated SIEM, and 24/7 detection & response — unified in a single pane of glass.
Map every device, application, and connection across your entire network without installing software on a single endpoint. IT, OT, and IoT — all visible in real time.
Connect to hundreds of IT and security products — firewalls, cloud platforms, OT systems, SaaS applications — maximizing your existing technology investments.
Palo Alto, Fortinet, Cisco, Meraki, and more
AWS, Azure, GCP, Microsoft 365, Google Workspace
CrowdStrike, SentinelOne, Microsoft Defender
Industrial control systems, medical devices, smart building
Every infrastructure element scored in real time using NIST Cybersecurity Framework guidelines. Prioritize what matters most based on your environment, industry cohort, and historical breach data.
Aggregate, correlate, and analyze log data from every source across your environment. Real-time alerting and compliance-ready reporting built in.
Ingest logs from every device, application, and cloud service in your environment with built-in parsers.
AI-driven correlation engine connects events across disparate sources to surface meaningful security signals.
Pre-built report templates for HIPAA, PCI-DSS, CMMC, and more. Scheduled delivery for audit readiness.
Powered by a proprietary database spanning 10+ years of historical threat data and carrier-grade infrastructure for global, real-time context and analysis.
AI-powered anomaly detection combined with 24/7 SOC operations. From alert triage to full remediation.
System generates risk ratings across applications, environments, and profiles to prioritize remediation efforts.
AI-powered detection algorithms backed by 24+ U.S. patents, providing complete network visibility with real-time relative risk assessment.